Terraform module to implements Multi-Account Log Archive.
English | 简体中文
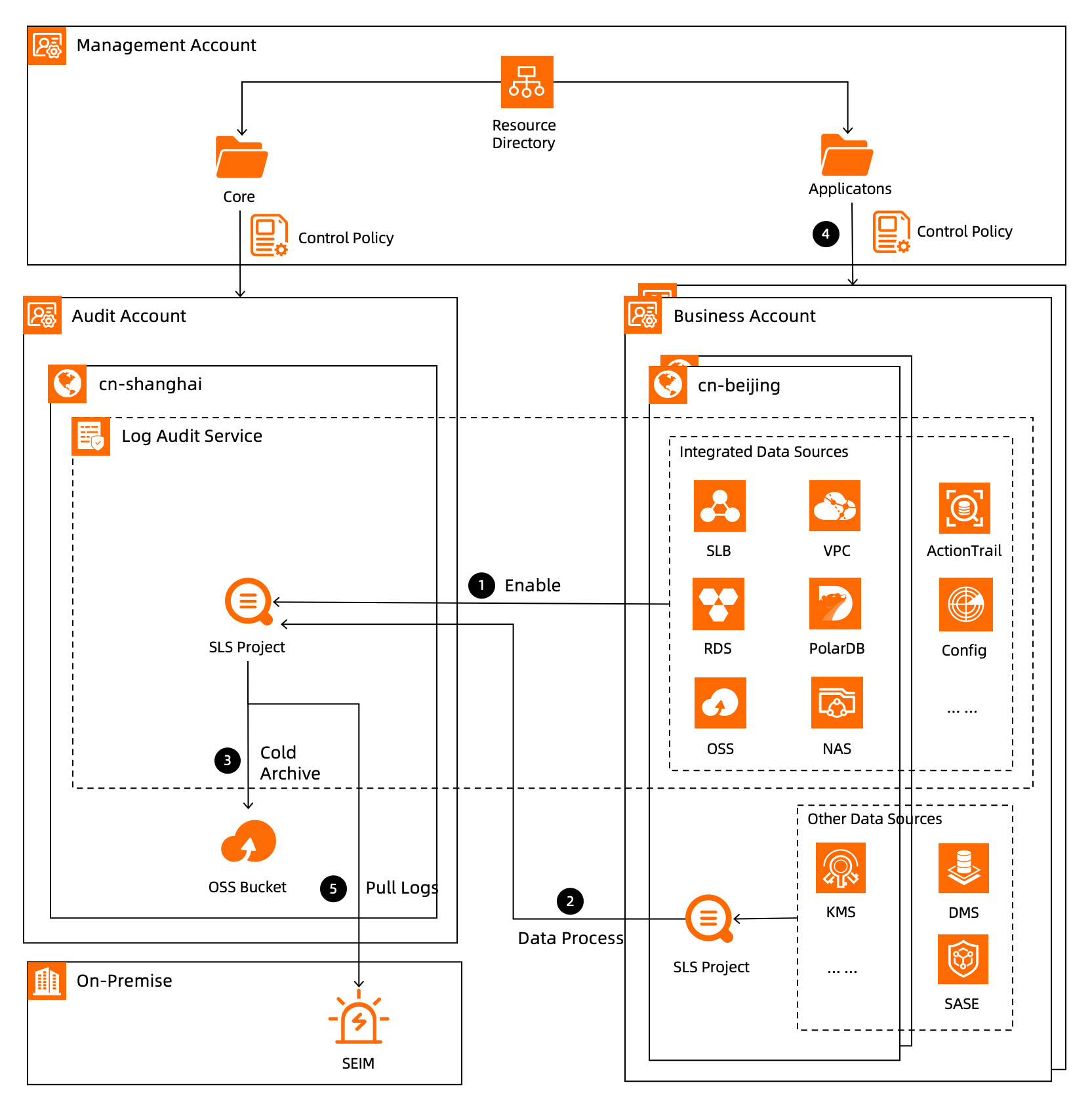
Log auditing is not only the basis of enterprise security compliance, but also a rigid requirement of laws and regulations. In a multi-account system, the unified collection and archiving of audit logs can not only ensure the implementation of relevant laws and regulations, but also is an important part of enterprise security protection.
This module is based on the log auditing of the SLS service, enabling the automated and unified collection and archiving of audit logs in the cloud. It meets the audit and security needs of enterprises on the cloud within a multi-account system.
- Built multi-account structure in Resource Directory.
- Enabled OSS service and SLS service in logarchive account.
You can use this in your terraform template with the following steps.
provider "alicloud" {
alias = "management_account"
region = "cn-hangzhou"
}
# assume role to logarchive account
provider "alicloud" {
alias = "log_archive_account"
region = "cn-hangzhou"
assume_role {
role_arn = format("acs:ram::%s:role/ResourceDirectoryAccountAccessRole", var.log_archive_account_id)
session_name = "LandingZoneLogAudit"
session_expiration = 3600
}
}
resource "random_string" "random" {
length = 8
special = false
upper = false
}
module "log_archive" {
source = "alibabacloud-automation/landing-zone-log-archive/alicloud"
providers = {
alicloud.management_account = alicloud.management_account
alicloud.log_archive_account = alicloud.log_archive_account
}
log_audit_display_name = format("landingzone-log-audit-%s", random_string.random.result)
log_audit_config = {
oss_access_enabled = "true"
oss_access_ttl = "7"
rds_enabled = "true"
rds_ttl = "180"
cloudfirewall_enabled = "true"
cloudfirewall_ttl = "180"
k8s_audit_enabled = "true"
k8s_audit_ttl = "180"
}
enabled_control_policy = true
control_policy_name = "ProhibitDeleteLogAudit"
control_policy_description = "Prohibit to delete resources for log archiving and auditing."
}
# cold archive to oss(optional)
module "cold_archive_to_oss" {
source = "alibabacloud-automation/landing-zone-log-archive/alicloud//modules/cold-archive-to-oss"
providers = {
alicloud = alicloud.log_archive_account
}
project_name = module.log_archive.log_archive_project_name
use_existed_bucket = false
bucket_name = format("landingzone-log-audit-%s", random_string.random.result)
bucket_storage_class = "ColdArchive"
bucket_redundancy_type = "LRS"
bucket_tags = {
"landingzone" : "logarchive"
}
bucket_force_destroy = true
bucket_resource_group_id = null
use_existed_archive_ram_role = false
archive_ram_role_name = "audit-log-cold-archive-role"
# Please configure the logstore you need to cold archiving
logstore_exports = [
{
logstore_name = "oss_log"
export_name = "cold_archive_oss_log"
display_name = "cold_archive_oss_log"
bucket_directory = "oss_log"
suffix = ""
buffer_interval = 300
buffer_size = 256
compress_type = "snappy"
time_zone = "+0800"
content_type = "json"
path_format = "%Y/%m/%d/%H/%M"
}
]
}| Name | Version |
|---|---|
| terraform | >= 1.3 |
| alicloud | >= 1.229.0 |
| Name | Version |
|---|---|
| alicloud.log_archive_account | >= 1.229.0 |
| alicloud.management_account | >= 1.229.0 |
No modules.
| Name | Type |
|---|---|
| alicloud_log_audit.log_archive | resource |
| alicloud_resource_manager_control_policy.log_archive | resource |
| alicloud_resource_manager_control_policy_attachment.log_archive | resource |
| alicloud_resource_manager_delegated_administrator.management | resource |
| alicloud_resource_manager_service_linked_role.log_archive | resource |
| alicloud_account.log_archive | data source |
| alicloud_ram_roles.log_archive | data source |
| alicloud_regions.log_archive | data source |
| alicloud_resource_manager_delegated_administrators.management | data source |
| Name | Description | Type | Default | Required |
|---|---|---|---|---|
| control_policy_description | The description of the control policy. | string |
"Prohibit to delete resources for log archiving and auditing." |
no |
| control_policy_name | The name of the control policy. | string |
"ProhibitDeleteLogAudit" |
no |
| enabled_control_policy | Whether to enable control policy to prohibit deletion of resources for log archiving and auditing. | bool |
true |
no |
| log_audit_config | Log audit detailed configuration. | object({ |
null |
no |
| log_audit_display_name | Name of SLS log audit. | string |
n/a | yes |
| Name | Description |
|---|---|
| log_archive_project_name | The namme of log archive project. |
| log_audit_id | The ID of the log audit. |
| resource_manager_delegated_administrator_id | The resource ID of Delegated Administrator. The value formats as <account_id>:<service_principal>. |
If you have any problems when using this module, please opening a provider issue and let us know.
Note: There does not recommend opening an issue on this repo.
Created and maintained by Alibaba Cloud Terraform Team(terraform@alibabacloud.com).
MIT Licensed. See LICENSE for full details.